A security researcher has dropped a zero-day remote code execution vulnerability on Twitter that works on the current version of Google Chrome and Microsoft Edge.
A zero-day vulnerability is a security bug that has been publicly disclosed but has not been patched in the released version of the affected software.
Today, security researcher Rajvardhan Agarwal released a working proof-of-concept (PoC) exploit for a remote code execution vulnerability for the V8 JavaScript engine in Chromium-based browsers.
1 day ago Indeed, he thinks Google Chrome’s change will inspire a further shift for advertisers to think about creating more diverse adverts that speak to underserved audiences. Google Chrome uses a process called Google Update to check for updates. Learn more about how Google Update works. Using a Chrome device at work.
Just here to drop a chrome 0day. Yes you read that right.https://t.co/sKDKmRYWBPpic.twitter.com/PpVJrVitLR
 — Rajvardhan Agarwal (@r4j0x00) April 12, 2021
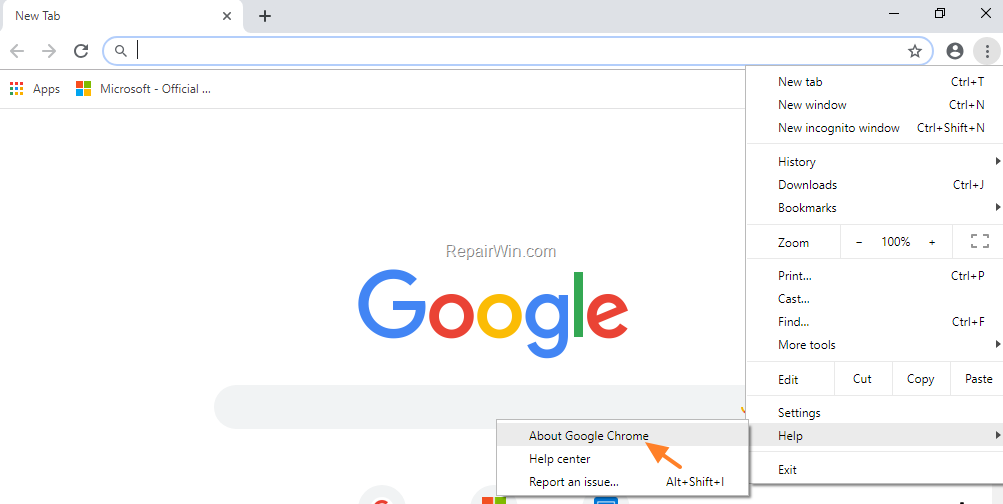
— Rajvardhan Agarwal (@r4j0x00) April 12, 2021While Agarwal states that the vulnerability is fixed in the latest version of the V8 JavaScript engine, it is not clear when Google will roll out the Google Chrome.
About Google Chrome Relaunch
When the PoC HTML file, and its corresponding JavaScript file, are loaded in a Chromium-based browser, it will exploit the vulnerability to launch the Windows calculator (calc.exe) program.
While no developer likes a zero-day release for their software, the good thing is that Agarwal's zero-day cannot currently escape the browser's sandbox. The Chrome sandbox is a browser security boundary that prevents remote code execution vulnerabilities from launching programs on the host computer.
For Agarwal's zero-day RCE exploit to work, it would need to be chained with another vulnerability that can allow the exploit to escape the Chromium sandbox.
To test the exploit, BleepingComputer launched the Microsoft Edge and Google Chrome browsers with the --no-sandbox flag, which turns off the Chromium sandbox.
With the sandbox disabled, we could use Agarwal's exploit to launch Calculator on our Windows 10 device. Our tests' exploitable versions are Google Chrome 89.0.4389.114 and Microsoft Edge 89.0.774.76, which are the latest versions in the Stable channel.
This vulnerability is believed to be the same one used by Dataflow Security's Bruno Keith and Niklas Baumstark at Pwn2Own 2021, where the researchers exploited Google Chrome and Microsoft Edge.
getting popped with our own bugs wasn't on my bingo card for 2021. not sure it was too smart of Google to add that regression test right away... https://t.co/e0RUlmbxRK
— Niklas B (@_niklasb) April 12, 2021Google is expected to release Chrome 90 to the Stable channel tomorrow, and we will have to see if the upcoming version includes a fix for this zero-day RCE vulnerability.
BleepingComputer has contacted Google about the zero-day but has not received a reply as of yet.

Related Articles:
About Google Chrome Help
Google uses cookies and data to:About Google Chrome Page
- Deliver and maintain services, like tracking outages and protecting against spam, fraud, and abuse
- Measure audience engagement and site statistics to understand how our services are used
- Improve the quality of our services and develop new ones
- Deliver and measure the effectiveness of ads
- Show personalized content, depending on your settings
- Show personalized or generic ads, depending on your settings, on Google and across the web
About Google Chromecast
For non-personalized content and ads, what you see may be influenced by things like the content you’re currently viewing and your location (ad serving is based on general location). Personalized content and ads can be based on those things and your activity like Google searches and videos you watch on YouTube. Personalized content and ads include things like more relevant results and recommendations, a customized YouTube homepage, and ads that are tailored to your interests.Click “Customize” to review options, including controls to reject the use of cookies for personalization and information about browser-level controls to reject some or all cookies for other uses. You can also visit g.co/privacytools anytime.
